Part of a High-Tech Security System Explained
Security used to be simple. A lock. A key. Maybe a guard who nodded when you walked in. That was it. But today? Security is everywhere and nowhere at the same time. Silent. Watching. Learning. Deciding. Every modern organization, home, data center, airport, hospital, and even smartphone relies on something far more complex. Something layered Something intelligent. Something that is part of a high-tech security system.
And here’s the strange part. Most people never notice it.
They walk through doors that open automatically They log into apps that instantly know it’s them. They move through cities filled with sensors and cameras that don’t feel intrusive, yet never sleep. This is not accidental This is design. This is technology quietly doing its job, without applause.
A high-tech security system is not one device. It’s a living network. And every component, every sensor, every algorithm, every silent check running in the background plays a role. A part. Sometimes small. Sometimes massive. But always critical.
Understanding What “ Part of a High- Tech Security System ” Really Means
When people hear the expression part of a high- tech security system, they frequently imagine a camera. Or a point scanner. Or perhaps facial recognition. That’s accessible. Those are visible. Palpable. Easy to point at.
But the reality is deeper.
A high-tech security system is an ecosystem. Hardware talks to software. Software talks to data. Data talks to artificial intelligence. And AI talks back, making decisions in milliseconds. One part alone does nothing impressive. Together? They create something powerful. Almost alive.
A motion sensor detecting movement at 3 a.m. That’s a part of a high-tech security system. A machine-learning model deciding whether that movement is a human, an animal, or just wind. Also part of it. The encrypted network sending that data securely to a control center. Still part of it. The automated alert sent to a phone. Yes. That too.
Remove one piece, and the system weakens. Sometimes it collapses.
The Shift From Physical to Intelligent Security
There was a time when security was reactive. Something happened. Then someone responded. A break-in. An alarm. A call to authorities. Late. Often too late.
High-tech security systems flipped that logic.
Now, systems predict. They analyze patterns. They notice anomalies They act before damage happens. Or at least try to. This shift didn’t happen overnight. It grew slowly. Camera by camera. Line of code by line of code.
A modern part of a high-tech security system doesn’t just observe. It interprets. It learns It adapts It asks questions like: Is this normal? Has this behavior happened before? Should I worry?
That’s not a simple sensor anymore. That’s intelligence embedded into security.
Sensors: The Eyes and Ears That Never Blink
Every high-tech security system starts with input. Sensors. Cameras. Microphones. Environmental detectors. These are the senses.
Motion sensors detect presence. Thermal sensors detect heat. Cameras capture visuals. LiDAR maps spaces. Even pressure sensors under floors can notice footsteps. All of these are parts of a high-tech security system, quietly feeding raw data into the brain.
But raw data alone is useless.
A camera sees everything. It doesn’t understand. That’s where the next layer comes in.
AI and Machine Learning: The Brain Behind the System
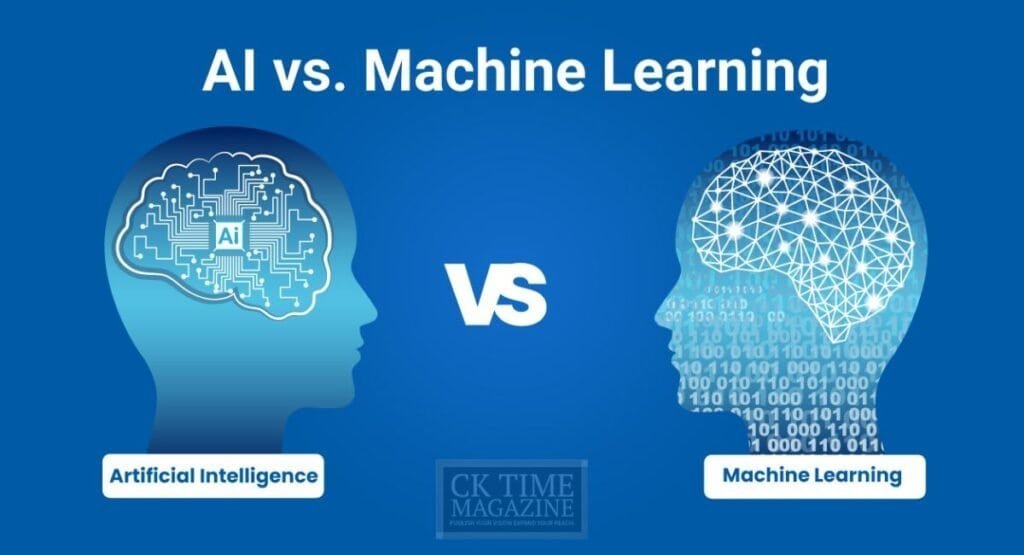
This is where security becomes smart. Artificial intelligence processes what sensors collect. Machine learning models compare it with historical data. Patterns emerge. Threats stand out.
A person walking into an office at 10 a.m. Normal. The same person entering at 3 a.m. Suspicious. Someone tailgating behind an employee through a secure door. Noticed. Flagged.
AI is now a core part of a high-tech security system. Without it, systems are blind despite having eyes. They would drown in data. AI filters noise from signal.
And the scary thing? It gets better over time. Learns mistakes. Refines accuracy. Sometimes without humans even noticing.
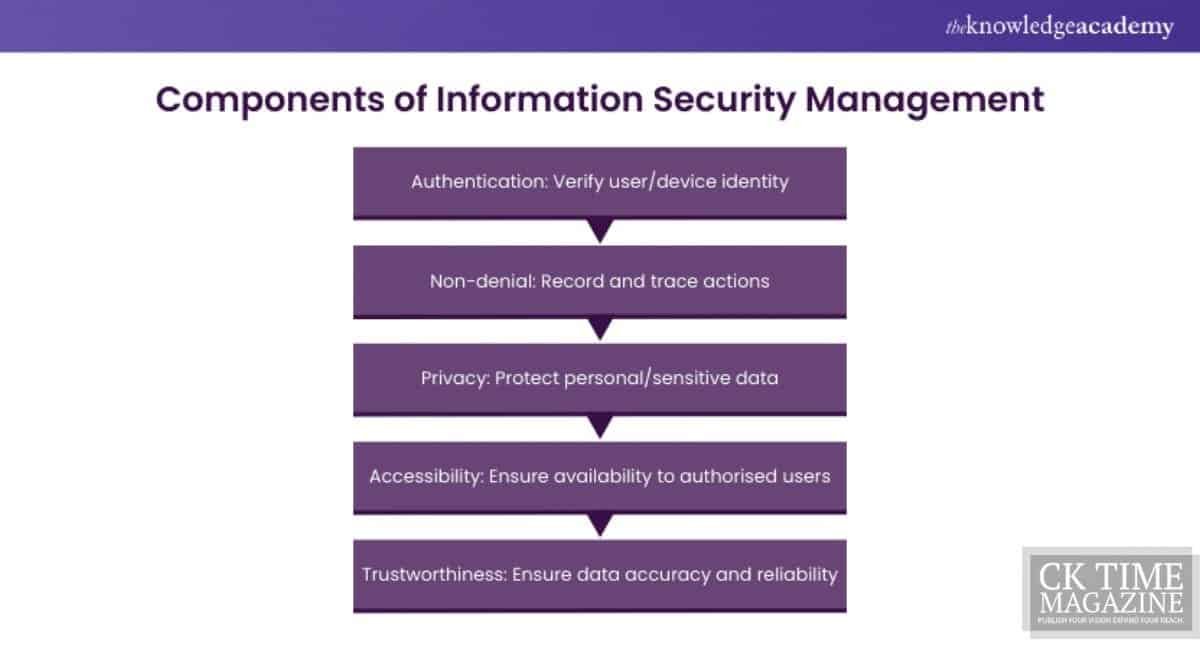
Access Control: Identity Is the New Perimeter
Walls don’t protect data anymore. Identity does.
Modern access control is one of the most critical parts of a high-tech security system. Passwords are fading. Biometrics are rising. Fingerprints. Facial recognition. Iris scans. Behavioral biometrics even analyze how you type or move your mouse.
You don’t just prove who you are once. The system keeps checking. Constantly. Quietly.
This is called continuous authentication. And it’s powerful. Because even if credentials are stolen, behavior is harder to fake. This layered identity verification is what protects banks, cloud platforms, and enterprise networks today.
Cybersecurity: The Invisible Battlefield
Not all security threats wear hoodies and break windows. Most never touch the physical world at all.
Cybersecurity is a massive, essential part of a high-tech security system. Firewalls. Intrusion detection systems. Endpoint protection. Zero-trust architectures. They all operate silently, blocking millions of attacks users never see.
A single malicious packet dropped by a firewall. A suspicious login blocked by anomaly detection. A phishing email stopped by AI. Each is a small action. A small part. But together, they protect entire digital infrastructures.
And here’s the thing. Cyber threats evolve daily. So the systems protecting against them must evolve faster. That’s why automation and AI are no longer optional. They are survival tools.
Encryption: The Silent Shield
Data moves constantly. Between devices Between servers Between countries. Without encryption, it’s exposed. Naked. Vulnerable.
Encryption is a foundational part of a high-tech security system. It doesn’t look impressive. No flashing lights. No alerts. Just math. Complex. Brutal. Beautiful math.
Whether it’s end- to- end encryption in messaging apps or translated databases in pall waiters, this subcaste ensures that indeed if data is interdicted, it remains useless to bushwhackers. It’s protection by obscurity? No. By design.
And when encryption fails, systems fail. Completely.
Integration: Where Everything Comes Together
A sensor alone is weak. AI alone is blind. Access control alone is limited. The real power comes from integration.
Modern high-tech security systems are integrated platforms. Physical security talks to cybersecurity. Access control links with HR systems. Cameras integrate with AI analytics. Everything shares context.
This integration allows faster decisions. Smarter responses. Fewer false alarms.
A badge swipe. A face scan. A login attempt. All connected. All evaluated together. That’s what makes each part of a high-tech security system more powerful than it could ever be alone.
Real-World Story: When One Small Part Saved Everything
Consider a data center. Massive. Loud. Expensive. Billions of dollars flowing through servers.
One night, a single temperature sensor noticed something odd. Just a slight increase. Nothing dramatic. But the AI noticed it didn’t match normal patterns. An alert was triggered. Engineers checked. A cooling unit was failing.
Without that one sensor. That one part of a high-tech security system. The servers could have overheated. Data lost. Services down. Chaos.
Security isn’t always about stopping attackers. Sometimes it’s about preventing disasters.
Mortal Element The Weakest and Strongest Link
Ironically, humans are both a vulnerability and a strength.
No system is fully autonomous. At least not yet. Humans design them. Monitor them. Respond to alerts. Make final decisions. Training, awareness, and policy enforcement are also parts of a high-tech security system, even if they aren’t technical.
Social engineering attacks target people, not machines. That’s why user education is security. Culture is security. Process is security.
Ignore the human element, and even the most advanced system will fail.
Scalability and the Cloud Era
High-tech security systems today must scale. Instantly. Cloud infrastructure changed everything.
Security components are now distributed. Cloud-based access control. AI running on remote servers. Data analyzed globally in real time. This allows organizations to grow without rebuilding security from scratch.
Cloud security posture management, identity federation, and centralized monitoring are now essential parts of a high-tech security system in modern enterprises.
Compliance, Privacy, and Ethics
With power comes responsibility. Security systems collect data. Sensitive data. Faces. Movements. Behaviors.
Regulations like GDPR, HIPAA, and ISO norms force systems to admire sequestration. Compliance tools, inspection logs, and concurrence operation are also corridor of a high- tech security system, though infrequently bandied.
Ethics matter. Transparency matters. Trust matters. Without them, security becomes surveillance. And that’s a dangerous line.
The Future: Adaptive, Predictive, Almost Invisible
Where is all this going?
Future security systems will be even quieter. Even smarter. More adaptive. Threats will be predicted before they form. Systems will self-heal. Components will update themselves. Human intervention will decrease.
Everypart of a high-tech security systemwill become more autonomous. More contextual. More aware.
And yet, most users will never notice. That’s the goal.
FAQs Part of a High- Tech Security System
Any element that contributes to discovery, forestallment, analysis, or response — similar as detectors, AI, encryption, access control, and monitoring tools.
Yes. Without AI, systems cannot scale or respond quickly enough to modern threats.
Absolutely. Modern systems integrate both for complete situational awareness.
Yes. pall- grounded results make advanced security affordable and scalable.
Only if poorly designed. Ethical frameworks and compliance controls protect user privacy.
Final Thought
A part of a high-tech security system is never just a part. It’s a promise. A silent agreement between technology and trust. Between innovation and safety. Between what we see and what protects us without being seen.
And that’s the real power.